Here is an old imagination.... but renewed now..
What will happens if ONE INDIAN RUPEE = FORTY-FIVE AMERICAN DOLLARS !!!
There's tremendous improvement in the economy of India. India's exports increase, imports decrease.
India becomes a super power as Economy is Power.
That is this.
Yes. From today on,
"ONE INDIAN RUPEE = FORTY-FIVE AMERICAN DOLLARS"
Imagine... from then, this may happen...
SCENE 1
Venue : Microsoft Corporation, New York, US
Some s/w engineers are seeing some photographs.
s/w engg 1 : What's that?
s/w engg 2 : Bob's photographs from India.
s/w engg 1 : Wow. Let me see. Which is this place?
s/w engg 3 : (Sees the photo) This is Ramanthapur, Hyderabad.
s/w engg 1 : Fundoo yaar! And what is this? He's got an TVS 50 also.
s/w engg 2 : Let me see (sees). Sexy yaar. This guy enjoys life man...
s/w engg 3 : You know how much a TVS 50 costs? Nearly 200K. Say it in
dollars...
s/w engg 2: Oops. We can't dream of such a thing here.
s/w engg 1 : Let's go to India & try for a job.
[Everybody excited.]
SCENE 2
Venue: Sun Microsystems, SanFrancisco, California, US
s/w engg 1: I'm with you man. My Visa is expected
anytime. Soon I will fly to India
s/w engg 2 : Ohhh.... When is the party?
s/w engg 1: When I get it on hand.
s/w engg 2: Where will you be working?
s/w engg 1 : I'll be working in Madhapur.
s/w engg 2 : Oh! Madhapur. Great yaar. where it is...
s/w engg 1 : It is in Hyderabad.
s/w engg 3 : Fundoo place yaar. Nice climate Not like
California. You’ll love the weather yaar. One of my
friends is in Jaipur,Rajasthan...He says it's the
ultimate place to live in. Cool maan.
s/w engg 2 : Who is the client yaar?
s/w engg 1: You know Municipal Corporation of Hyderabad?
s/w engg 3 : Yeah. MCH. One of my friends is there in the Road Cleaning
Division. Most challenging job yaar. People are working in the cutting
edge of technology there.
s/w engg 1 : I'll be writing software for the accounts department of the
GCU.
s/w engg 2: GCU? what it means...?
s/w engg 1 : that is Garbage Collecting Unit.
s/w engg 3 : : Great yaar. That's what I like about that country. You can
get a job which requires all your skill. Not like here. See I'm writing
software for the space shuttle remote control.I hate this.
s/w engg 1 : Don't worry guys. I'll give you my Hotmail id. You can send
your resume to me and I'll forward it to the HRD.
[Everybody takes down his Hotmail id.]
SCENE 3
Venue: IBM, New York, US
(Conversation between a Male s/w engg. and Female s/w engg.)
Male : Hi!
Female: Hi. You know. I'm planning to settle in India soon.
Male : What??
Female : Yeah. My marriage will be here in America
only. He is doing his Ph.D in Miyapur College and he's coming here for a
month. His study will be over in 2 months. He's already got a job in MEB
(Miyapur Electricity Board). We planned to settle in Miyapur itself... I'm
also planning to work there. Let's see...
Male: Good luck... dont forget us & US...
SCENE 4
Venue: Intel Corp. US
s/w engg 1: Great news guys. Our George has got admission in the Nizam
College in Hyd with scholarship for B.A History. A great new field
yaar...
All are excited...
George : Got my Visa yesterday. It's all finalized now.
s/w engg 2 : Congrats yaar. So you are out of this country.
S/w engg 1 : B.A in Histroy...ohh...man, enjoy your life there?
s/w engg 2 : : Got full aid, eh?
George : Yeah. Got the UGC scholarship That will be 1200 Rupees per Year.
s/w engg 1 : Great. Enjoy.
s/w engg 2 : (Thinking loud): 1200 Indian Rupees...!
that means 1200 * 45 = 54000 Dollars... with that
amount I can buy a three bed-room flat & a Mercedes here...!!!
Monday, April 26, 2010
Sunday, April 25, 2010
How to disable and re-enable hibernation on a computer that is running Windows Vista
The Hiberfil.sys hidden system file is located in the root folder of the drive where the operating system is installed. The Windows Kernel Power Manager reserves this file when you install Microsoft Windows. The size of this file is approximately equal to the amount of random access memory (RAM) that is installed on the computer.
The computer uses the Hiberfil.sys file to store a copy of the system memory on the hard disk when the hybrid sleep setting is turned on. If this file is not present, the computer cannot hibernate.
Hibernation is made unavailable when you set the value of the Hibernate after setting to Never by using the Power Options item in Control Panel.
To make hibernation unavailable, follow these steps:
1) Click Start, and then type cmd in the Start Search box.
2) In the search results list, right-click Command Prompt, and then click Run as Administrator.
3) When you are prompted by User Account Control, click Continue.
4) At the command prompt, type powercfg.exe /hibernate off, and then press ENTER.
5) Type exit, and then press ENTER.
To make hibernation available, follow these steps:
1) Click Start, and then type cmd in the Start Search box.
2) In the search results list, right-click Command Prompt, and then click Run as Administrator.
3) When you are prompted by User Account Control, click Continue.
4) At the command prompt, type powercfg.exe /hibernate on, and then press ENTER.
5) Type exit, and then press ENTER to close the Command Prompt window.
Note:- The same process should also work for Windows 7.
Source: Microsoft site
Your computer needs more memory????
There comes a time when you just don't have enough memory. In the very beginning, everything was perfectly fine. Then after a few years of use, your desktop or laptop computer starts running slower and slower. Sometimes you are simply surfing the Internet, doing word processing, or listening to your music collection while running other applications, and suddenly your computer can’t keep up.
If your hard drive's activity light is blinking furiously, it means the drive is way too busy and, it is about time to install more memory (RAM). To understand why, just think of the computer's CPU as a chef, its hard drive as a refrigerator, and the RAM as a kitchen countertop. To cook a meal, the chef (CPU) has to take out the necessary ingredients (data) from the refrigerator (hard drive), and works with cooking gadgets on the countertop (RAM). As orders (applications) increase, more working space is therefore required.
So what takes up the most countertop space (memory) on your computer? Take Windows XP for example. Entering the desktop will take up 300 to 500 MB of memory, while opening a popular Flash game on FACEBOOK will need at least 250MB more. Even two Flash games can eat up 1GB of precious memory! It's lucky that you don't have to upgrade your whole computer to get more space, though. Instead, adding more RAM to your computer is much easier and more cost effective.
Usually a desktop computer has two to four memory slots, and a laptop has two. For most of users, 1.5GB to 2GB of memory will be sufficient. Before you install extra RAM, make sure that the memory you add is identical to that already in your computer. Lastly, be smart and choose a trustworthy brand.
(source: Transcend ePaper)
If your hard drive's activity light is blinking furiously, it means the drive is way too busy and, it is about time to install more memory (RAM). To understand why, just think of the computer's CPU as a chef, its hard drive as a refrigerator, and the RAM as a kitchen countertop. To cook a meal, the chef (CPU) has to take out the necessary ingredients (data) from the refrigerator (hard drive), and works with cooking gadgets on the countertop (RAM). As orders (applications) increase, more working space is therefore required.
So what takes up the most countertop space (memory) on your computer? Take Windows XP for example. Entering the desktop will take up 300 to 500 MB of memory, while opening a popular Flash game on FACEBOOK will need at least 250MB more. Even two Flash games can eat up 1GB of precious memory! It's lucky that you don't have to upgrade your whole computer to get more space, though. Instead, adding more RAM to your computer is much easier and more cost effective.
Usually a desktop computer has two to four memory slots, and a laptop has two. For most of users, 1.5GB to 2GB of memory will be sufficient. Before you install extra RAM, make sure that the memory you add is identical to that already in your computer. Lastly, be smart and choose a trustworthy brand.
(source: Transcend ePaper)
Five Reasons Why Solid State Drives (SSDs) Are Right for You
It is a well known fact that solid state drives are an emerging technology that has huge market potential. But how do SSDs differ from regular hard disk drives (HDD), and why do they deserve a place in your notebook or desktop PC?
Reason # 1: Lightning-fast data transfer
Speed matters when it comes to business and entertainment. With virtually instant access times of less than one millisecond, SSDs enable operating systems and commonly used software applications like web browsers to open faster and run more smoothly, thus creating an overall more enjoyable and lag-free computing experience.
Reason # 2: Lower system temperatures
Imaging working on your laptop in comfort, without the heat. In contrast to regular hard disk drives that are constantly in motion within the drive, which creates plenty of heat, SSD's cool-running stable operation equates to lower temperatures within the computer.
Reason # 3: Longer battery run-time
Still carrying a laptop AC adapter around in case your notebook battery runs out unexpectedly? Now you don’t have to. Compared to old-fashioned hard drives, SSDs consume roughly much less power when transferring data, and require less than 1W when idle. In short, an SSD will make your computer consume less power overall, which can significantly improve battery life when used in a notebook computer.
Reason # 4: Resistant to shock and vibration
Never underestimate the potential data corruption caused from excessive vibration, shock, or impact. Unlike regular hard drives, SSDs contain no spinning disks, spindles or any other fragile mechanical components. Therefore, there is nothing to break loose, get misaligned or become unreadable in case the drive is accidentally bumped or dropped. Your files will finally get the thorough protection they deserve.
Reason # 5: No more annoying hard drive noise
Sometimes you just need a quiet place to concentrate on your work. At times like these, any possible tiny noise will drive you crazy. While traditional hard drives tend to make a buzzing sound because of the vibrations when the spinning disks resonate through the case of your computer, SSDs can be 100% noise free since there are no mechanical moving parts inside.
(source: Transcend ePaper)
Reason # 1: Lightning-fast data transfer
Speed matters when it comes to business and entertainment. With virtually instant access times of less than one millisecond, SSDs enable operating systems and commonly used software applications like web browsers to open faster and run more smoothly, thus creating an overall more enjoyable and lag-free computing experience.
Reason # 2: Lower system temperatures
Imaging working on your laptop in comfort, without the heat. In contrast to regular hard disk drives that are constantly in motion within the drive, which creates plenty of heat, SSD's cool-running stable operation equates to lower temperatures within the computer.
Reason # 3: Longer battery run-time
Still carrying a laptop AC adapter around in case your notebook battery runs out unexpectedly? Now you don’t have to. Compared to old-fashioned hard drives, SSDs consume roughly much less power when transferring data, and require less than 1W when idle. In short, an SSD will make your computer consume less power overall, which can significantly improve battery life when used in a notebook computer.
Reason # 4: Resistant to shock and vibration
Never underestimate the potential data corruption caused from excessive vibration, shock, or impact. Unlike regular hard drives, SSDs contain no spinning disks, spindles or any other fragile mechanical components. Therefore, there is nothing to break loose, get misaligned or become unreadable in case the drive is accidentally bumped or dropped. Your files will finally get the thorough protection they deserve.
Reason # 5: No more annoying hard drive noise
Sometimes you just need a quiet place to concentrate on your work. At times like these, any possible tiny noise will drive you crazy. While traditional hard drives tend to make a buzzing sound because of the vibrations when the spinning disks resonate through the case of your computer, SSDs can be 100% noise free since there are no mechanical moving parts inside.
(source: Transcend ePaper)
Installing Windows xP after Windows Vista / 7
Requirements before proceeding:-
1) Installtion CD (and CD key/ serial number) of Windows xP.
2) Installtion DVD (and DVD key / serial number) of Winows vista.
3) Make sure that AC power supply is continuously available during the process.
4) Print the instructions if you feel it necessary.
Step 1:- Create a back-up of your all data (e.g. documents,pictures,software installers (installers not installed files!!!), etc.) whatever you don't want to loose in case of a problem. You can do it by just copy and paste operation to any external hard-disk or you can even burn them into DVDs or CDs.
Step 2:-Install xp as usual (preferably install it in the drive-partition other than that with vista or 7. For knowing how to create drive partitions, refer to Help and Support in Control panel. I hope there you should get enough information.)
Step 3:- When you will reboot the system after finishing the xP installation, you will see only xP and no trace of Vista. You don't need to worry at all if this occurs. Actually, this occurs because the boot-loader of xP does not recognise Vista (as it is a new Operating system which is a succesor to xP.). But Vista's boot-loader can recognize xP and we will make use of this fact in our process.
Step 4:- Insert the vista DVD and reboot. When asked for pressing any key to boot from CD or DVD... do it. In the window where it asks for installing vista, in the same window in lower side there is an option of correcting/reapiring the problems. When ypu find it , click to access it. It will automatically find your vista installation. Select you vista partition and continue. In the next window you will see an option of Reapairing start-up problems automatically. Select it and reboot after the process finishes when it asks so (In the log window you should see some repair has taken place).
Step 5:- When you reboot your vista should boot normally and this time you will see no trace of xP.
Step 6:- Editing boot.ini.
In Vista, the boot.ini is not editable directly, as the file itself is hard to locate, so we will be modifying it through "Boot Configuration Data Store Editor" bcdedit.exe:
a) first open a command prompt with administrative privilages (right-click and choose "run as administrator")
*Note:- the following 2 answers from bcdedit for each item are acceptable:
"The Operation Completed Successfully"
"The Specified Entry Already Exists"
b) Be sure to type each line carefully (replace C in the first line with the drive containing your Vista installation) (Just as an explanation, the loader type for XP is an NT Loader, hence the use of ntldr) :
bcdedit –set {ntldr} device partition=C:
bcdedit –set {ntldr} path \ntldr
bcdedit –displayorder {ntldr} –addlast
bcdedit -set {ntldr} description "Microsoft Windows XP"
c) This will correctly add XP to your boot sequence, and even name it properly instead of "Earlier Version of Windows".
d) the displayorder line also allows the entry to be visible under the advanced settings of your computer properties.
e) Vista is the default boot, if you wish to change this to XP it can be done by setting {current} to addlast, or under the computer
-> properties -> advanced settings.
f) If all done properly, XP and Vista will dual boot properly!
enjoy!!!
Note:-The above process is tested well with vista and should also work for Windows 7.You have to just read Vista as 7 in above explanation.
1) Installtion CD (and CD key/ serial number) of Windows xP.
2) Installtion DVD (and DVD key / serial number) of Winows vista.
3) Make sure that AC power supply is continuously available during the process.
4) Print the instructions if you feel it necessary.
Step 1:- Create a back-up of your all data (e.g. documents,pictures,software installers (installers not installed files!!!), etc.) whatever you don't want to loose in case of a problem. You can do it by just copy and paste operation to any external hard-disk or you can even burn them into DVDs or CDs.
Step 2:-Install xp as usual (preferably install it in the drive-partition other than that with vista or 7. For knowing how to create drive partitions, refer to Help and Support in Control panel. I hope there you should get enough information.)
Step 3:- When you will reboot the system after finishing the xP installation, you will see only xP and no trace of Vista. You don't need to worry at all if this occurs. Actually, this occurs because the boot-loader of xP does not recognise Vista (as it is a new Operating system which is a succesor to xP.). But Vista's boot-loader can recognize xP and we will make use of this fact in our process.
Step 4:- Insert the vista DVD and reboot. When asked for pressing any key to boot from CD or DVD... do it. In the window where it asks for installing vista, in the same window in lower side there is an option of correcting/reapiring the problems. When ypu find it , click to access it. It will automatically find your vista installation. Select you vista partition and continue. In the next window you will see an option of Reapairing start-up problems automatically. Select it and reboot after the process finishes when it asks so (In the log window you should see some repair has taken place).
Step 5:- When you reboot your vista should boot normally and this time you will see no trace of xP.
Step 6:- Editing boot.ini.
In Vista, the boot.ini is not editable directly, as the file itself is hard to locate, so we will be modifying it through "Boot Configuration Data Store Editor" bcdedit.exe:
a) first open a command prompt with administrative privilages (right-click and choose "run as administrator")
*Note:- the following 2 answers from bcdedit for each item are acceptable:
"The Operation Completed Successfully"
"The Specified Entry Already Exists"
b) Be sure to type each line carefully (replace C in the first line with the drive containing your Vista installation) (Just as an explanation, the loader type for XP is an NT Loader, hence the use of ntldr) :
bcdedit –set {ntldr} device partition=C:
bcdedit –set {ntldr} path \ntldr
bcdedit –displayorder {ntldr} –addlast
bcdedit -set {ntldr} description "Microsoft Windows XP"
c) This will correctly add XP to your boot sequence, and even name it properly instead of "Earlier Version of Windows".
d) the displayorder line also allows the entry to be visible under the advanced settings of your computer properties.
e) Vista is the default boot, if you wish to change this to XP it can be done by setting {current} to addlast, or under the computer
-> properties -> advanced settings.
f) If all done properly, XP and Vista will dual boot properly!
enjoy!!!
Note:-The above process is tested well with vista and should also work for Windows 7.You have to just read Vista as 7 in above explanation.
Numerology
1. The Originator
1's are originals. Coming up with new ideas and executing them is natural. Having things their own way is another trait that gets them labeled as being stubborn and arrogant. 1's are extremely honest and do well to learn some diplomacy skills. They like to take the initiative and are often leaders or bosses, as they like to be the best. Being self-employed is definitely helpful for them. Lesson to learn: Others' ideas might be just as good or better and to stay open minded.
2. The Peacemaker
2's are the born diplomats. They are aware of others' needs and moods and often think of others before themselves. Naturally analytical and very intuitive they don't like to be alone. Friendship and companionship is very important and can lead them to be successful in life, but on the other hand they'd rather be alone than in an uncomfortable relationship. Being naturally shy they should learn to boost their self-esteem and express themselves freely and seize the moment and not put things off.
3. The Life of the Party
3's are idealists. They are very creative, social, charming, romantic, and easygoing. They start many things, but don't always see them through. They like others to be happy and go to great lengths to achieve it. They are very popular and idealistic. They should learn to see the world from a more realistic point of view.
4. The Conservative
4's are sensible and traditional. They like order and routine. They only act when they fully understand what they are expected to do. They like getting their hands dirty and working hard. They are attracted to the outdoors and feel an affinity with nature. They are prepared to wait and can be stubborn and persistent. They should learn to be more flexible and to be nice to themselves.
5. The Nonconformist
5's are the explorers. Their natural curiosity, risk taking, and enthusiasm often lands them in hot water. They need diversity, and don't like to be stuck in a rut. The whole world is their school and they see a learning possibility in every situation. The questions never stop. They are well advised to look before they take action and make sure they have all the facts before jumping to conclusions.
6. The Romantic
6's are idealistic and need to feel useful to be happy. A strong family connection is important to them. Their emotions influence their decisions. They have a strong urge to take care of others and to help. They are very loyal and make great teachers. They like art or music. They make loyal friends who take the friendship seriously. 6's should learn to differentiate between what they can change and what they cannot.
7. The Intellectual
7's are the searchers. Always probing for hidden information, they find it difficult to accept things at face value. Emotions don't sway their decisions. Questioning everything in life, they don't like to be questioned themselves. They're never off to a fast start, and their motto is slow and steady wins the race. They come across as philosophers and being very knowledgeable, and sometimes as loners. They are technically inclined and make great researchers uncovering information. They like secrets. They live in their own world and should learn what is acceptable and what not in the world at large.
8. The Big Shot
8's are the problem solvers. They are professional, blunt and to the point, have good judgment and are decisive. They have grandiose plans and like to live the good life. They are take charge people. They view people objectively. They let you know in no uncertain terms that they are the boss. They should learn to base their decisions on their own needs rather than on what others want.
9. The Performer
9's are natural entertainers. They are very caring and generous, giving away their last dollar to help. With their charm they have no problem making friends and nobody is a stranger to them. They have so many different personalities that people around them have a hard time understanding them. They are like chameleons, ever changing and blending in. They have tremendous luck, but also can suffer from extremes in fortune and mood. To be successful they need to build a loving foundation.
1's are originals. Coming up with new ideas and executing them is natural. Having things their own way is another trait that gets them labeled as being stubborn and arrogant. 1's are extremely honest and do well to learn some diplomacy skills. They like to take the initiative and are often leaders or bosses, as they like to be the best. Being self-employed is definitely helpful for them. Lesson to learn: Others' ideas might be just as good or better and to stay open minded.
2. The Peacemaker
2's are the born diplomats. They are aware of others' needs and moods and often think of others before themselves. Naturally analytical and very intuitive they don't like to be alone. Friendship and companionship is very important and can lead them to be successful in life, but on the other hand they'd rather be alone than in an uncomfortable relationship. Being naturally shy they should learn to boost their self-esteem and express themselves freely and seize the moment and not put things off.
3. The Life of the Party
3's are idealists. They are very creative, social, charming, romantic, and easygoing. They start many things, but don't always see them through. They like others to be happy and go to great lengths to achieve it. They are very popular and idealistic. They should learn to see the world from a more realistic point of view.
4. The Conservative
4's are sensible and traditional. They like order and routine. They only act when they fully understand what they are expected to do. They like getting their hands dirty and working hard. They are attracted to the outdoors and feel an affinity with nature. They are prepared to wait and can be stubborn and persistent. They should learn to be more flexible and to be nice to themselves.
5. The Nonconformist
5's are the explorers. Their natural curiosity, risk taking, and enthusiasm often lands them in hot water. They need diversity, and don't like to be stuck in a rut. The whole world is their school and they see a learning possibility in every situation. The questions never stop. They are well advised to look before they take action and make sure they have all the facts before jumping to conclusions.
6. The Romantic
6's are idealistic and need to feel useful to be happy. A strong family connection is important to them. Their emotions influence their decisions. They have a strong urge to take care of others and to help. They are very loyal and make great teachers. They like art or music. They make loyal friends who take the friendship seriously. 6's should learn to differentiate between what they can change and what they cannot.
7. The Intellectual
7's are the searchers. Always probing for hidden information, they find it difficult to accept things at face value. Emotions don't sway their decisions. Questioning everything in life, they don't like to be questioned themselves. They're never off to a fast start, and their motto is slow and steady wins the race. They come across as philosophers and being very knowledgeable, and sometimes as loners. They are technically inclined and make great researchers uncovering information. They like secrets. They live in their own world and should learn what is acceptable and what not in the world at large.
8. The Big Shot
8's are the problem solvers. They are professional, blunt and to the point, have good judgment and are decisive. They have grandiose plans and like to live the good life. They are take charge people. They view people objectively. They let you know in no uncertain terms that they are the boss. They should learn to base their decisions on their own needs rather than on what others want.
9. The Performer
9's are natural entertainers. They are very caring and generous, giving away their last dollar to help. With their charm they have no problem making friends and nobody is a stranger to them. They have so many different personalities that people around them have a hard time understanding them. They are like chameleons, ever changing and blending in. They have tremendous luck, but also can suffer from extremes in fortune and mood. To be successful they need to build a loving foundation.
World's smallest superconductor found, and it's less than 1nm wide
Scientists at the University of Ohio have discovered what they claim to be the world’s smallest superconductor, which is less than 1nm in width. The superconductor works on a molecular scale and is formed by four pairs of molecules. The research was published in Nature’s Nanotechnology paper, and has been called a path-breaking idea in the field of nanoscale electronics.
In the past, interconnects of the modern chip fabrication process have always had problems with Joule heating and melting, as they traditionally have been built by metal, which conducts heat equally well as electricity. Interconnects on the nanoscale are called nanowires, whose electrical resistance unfortunately increases as they are made smaller.
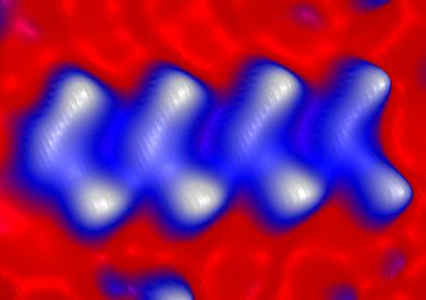
Figure:- The 4 molecule chain that is the world's smallest superconductor
However, using the new world’s smallest superconductor as the basis for a new-generation of nanowires might remove this problem altogether. Superconductors are so named because their electrical resistance tends towards zero, and will conduct electricity while only negligibly causing heat or power loss. The breakthrough comes with the fact that a certain superconductor is now known to be able to function on the molecular level, completely at odds with what scientists thought was a unshakeable truth, that superconductors only functioned on the macroscopic level.
These findings will have tremendous applications in nanoscale electronics, most notably in microprocessor design and fabrication.
Source: Think Digit
"Mind-reading" brain-scan software showcased in NY
Mind-reading brain-scan software showcased in NY
NEW YORK — Mind reading may no longer be the domain of psychics and fortune tellers — now some computers can do it, too.
Software that uses brain scans to determine what items people are thinking about was among the technological innovations showcased Wednesday by Intel Corp., which drew back the curtain on a number of projects that are still under development.
The software analyzes functional MRI scans to determine what parts of a person's brain is being activated as he or she thinks. In tests, it guessed with 90 percent accuracy which of two words a person was thinking about, said Intel Labs researcher Dean Pomerleau.
Eventually, the technology could help the severely physically disabled to communicate. And Pomerleau sees it as an early step toward one day being able to control technology with our minds.
"The vision is being able to interface to information, to your devices and to other people without having an intermediary device," he said.
For now, the project's accomplishments are far more modest — it can only be used with prohibitively expensive and bulky fMRI equipment and hasn't yet been adapted to analyze abstract thoughts.
The system works best when a person is first scanned while thinking of dozens of different concrete nouns — words like "bear" or "hammer." When test subjects are then asked to pick one of two new terms and think about it, the software uses the earlier results as a baseline to determine what the person is thinking.
The software works by analyzing the shared attributes of different words. For example, a person who is thinking of a bear uses the same parts of the brain that light up when he or she thinks of a puppy or something else furry. A person thinking of a bear also shows activity in the amygdala — home of the fight-or-flight response.
While Intel primarily makes computer processors and other hardware, it often works to develop and demonstrate new technologies in an effort to stimulate the market and advance its reputation.
Music reduces stress in heart disease patients
Washington, April 13 (IANS): Listening to music may benefit patients who suffer severe stress and anxiety associated with having and undergoing treatment for coronary heart disease (CHD).
A study found that listening to music could decrease blood pressure, heart rate and levels of anxiety in heart patients.
Living with heart disease is extremely stressful. The uncertainties and anxieties surrounding diagnosis and the various medical procedures involved in treatment can significantly worsen the condition.
For example, stress can increase blood pressure, leading to increased risk of complications. Music listening may help to alleviate stress and therefore reduce this risk.
'Our findings suggest music listening may be beneficial for heart disease patients,' says Joke Bradt, who works at the Arts and Quality of Life Research Centre at Temple University, Philadelphia.
The researchers reviewed data from 23 studies which together included 1,461 patients. Two studies focused on patients treated by trained music therapists, but most did not, using instead interventions where patients listened to pre-recorded music on CDs offered by healthcare professionals.
Listening to music provided some relief for CHD patients suffering from anxiety, by reducing heart rate and blood pressure.
There was also some indication that music listening improved mood, although no improvement was seen for patients suffering from depression due to the disease, said a Temple University release.
'We all know that music can impact on our emotions, our physiological responses, as well as our outlook on life, and this early research shows that it is well worth finding out more about how it could help heart disease patients.'
These findings were published in Cochrane Systematic Review.
Indo Asian News Service
A study found that listening to music could decrease blood pressure, heart rate and levels of anxiety in heart patients.
Living with heart disease is extremely stressful. The uncertainties and anxieties surrounding diagnosis and the various medical procedures involved in treatment can significantly worsen the condition.
For example, stress can increase blood pressure, leading to increased risk of complications. Music listening may help to alleviate stress and therefore reduce this risk.
'Our findings suggest music listening may be beneficial for heart disease patients,' says Joke Bradt, who works at the Arts and Quality of Life Research Centre at Temple University, Philadelphia.
The researchers reviewed data from 23 studies which together included 1,461 patients. Two studies focused on patients treated by trained music therapists, but most did not, using instead interventions where patients listened to pre-recorded music on CDs offered by healthcare professionals.
Listening to music provided some relief for CHD patients suffering from anxiety, by reducing heart rate and blood pressure.
There was also some indication that music listening improved mood, although no improvement was seen for patients suffering from depression due to the disease, said a Temple University release.
'We all know that music can impact on our emotions, our physiological responses, as well as our outlook on life, and this early research shows that it is well worth finding out more about how it could help heart disease patients.'
These findings were published in Cochrane Systematic Review.
Indo Asian News Service
Top 6 ways to beat computer viruses
Computer viruses
They’ve been around for years, and they aren’t going away. And they continue to proliferate and cause major damage, with the “Gumblar” or “Geno” virus as the latest high-profile virus to infect computers.
This virus is a particularly insidious one, with a multi-phased attack. After infecting a machine, Gumblar installs a series of malware programs, including a small application capable of stealing FTP credentials. It can gain control of an entire website and freely operate it.
Gumblar also monitors the infected user’s online activity, and waits for the user to conduct Google searches. The malware hijacks the search results, replacing them with any link of its choice and further infecting the computer with malware. The virus also installs a fake antivirus program known as System Security 2009, and disables any legitimate security software.
So what can you do to avoid becoming a victim of this and other viruses? Here are the top strategies to follow:
1. Be sure to install updates for Microsoft® products
Using Microsoft Update with automatic updating is a strong – and simple to implement – first line of defence against security threats. The Microsoft Update site scans your computer and gives you a list of updates that are relevant to your computer and its configuration.
2. Install the latest versions of Adobe Reader and Flash Player
The Gumblar virus takes advantage of common Adobe Reader, Adobe Acrobat, and Adobe Shockwave Flash Player vulnerabilities, which lead to the download of additional malicious files. Keeping these programs up-to-date can help ensure you’ve got the latest and most secure versions available.
3. Create and maintain strong passwords
Keeping and using strong passwords, and changing them regularly, is a very important step in keeping your online accounts, computer files and personal information secure. Ideally, passwords should be long and use the entire keyboard, not just the letters and characters you use or see most often.
4. Invest in quality antivirus and antispyware protection
While it isn’t a 100% guarantee of security, your risk of virus infection is significantly lower when you use a comprehensive antivirus protection program. Without some sort of protection, you are virtually guaranteed to become a victim of viruses, spyware and spam.
5. Don’t click on unknown links or attachments
Never click on any unfamiliar links embedded in an e-mail, or open attachments from unknown senders. And check for anything unusual even in links you do recognise; slightly altered domain names could indicate that a site has been hijacked.
6. Download files only from trusted sites
You should only download files from known, well-established sources. Never download anything if you’re not certain what it is. When in doubt, don't download the file to your computer at all: download it onto an external drive or USB stick, and then check the files with antivirus scanning software.
Lock Your Drives and Folders Using Registry Tweaks
Lock Your Drives and Folders Using Registry Tweaks
There are plenty of software which locks drives and folder to protect your confidential data. Why waste money on such tools when you can do it with a simple registry tweak? Here’s how:Caution: Before you attempt these tweaks, please make sure that you have a backup of your registry, just incase something goes wrong in the middle.
Locking Folders:
Consider you want to lock a folder named XXXX in your E:\, whose path is E:\XXXX.Now open the Notepad and type the following
ren xxxx xxxx.{21EC2020-3AEA-1069-A2DD-08002B30309D}
Where xxxx is your folder name. Save the text file as loc.bat in the same drive.
Open another new notepad text file and type the following
ren xxxx.{21EC2020-3AEA-1069-A2DD-08002B30309D} xxxx
Save the text file as key.bat in the same drive.
Steps to lock the folder:
To lock the xxxx folder, simply click the loc.bat and it will transform into control panel icon which is inaccessible.
To unlock the folder click the key.bat file. Thus the folder will be unlocked and the contents are accessible.
Locking Drives:
We don’t usually prefer to lock our drives, but sometimes it becomes nesscary. Say for instance you might have stored your office documents in D:\ and you don’t want your kids to access it, in such case this technique can be useful for you. Please don’t try this tweak with your root drive (usually C:\ is the root drive) since root drives are not intended to be locked because they are mandatory for the system and application programs.Start & Run and type Regedit to open Registry editor.
Browse HKEY_CURRENT_USER\Software\Microsoft\Windows\Curre ntVersion\Policies\Explorer
Create a new DWORD value NoViewOnDrive and set its value as 2^ (Alpha Number of Drive Letter-1) where Alpha number are simple counting of alphabets from A to Z as 1 - 26
For example: to lock C:\, Alpha number of C is 3 so 2^ (3-1) = 4 (decimal value)
To lock more drives, calculate the value of each drive and then set sum of those numbers as value.
To unlock your drive just delete the key from the registry.
About Unicode
Unicode
We all almost have been using notepad ( for Windows OS) and gedit ( for Linux and Unix Users) . When we saving files in these editors, in the save pop up window, there will be a option Called "Unicode Format".. How many of us wanted to know. Here is a small description and usage about it.. Please go through when u find time.
What is Unicode?
Unicode provides a unique number for every character, no matter what the platform, no matter what the program, no matter what the language.Fundamentally, computers just deal with numbers. They store letters and other characters by assigning a number for each one. Before Unicode was invented, there were hundreds of different encoding systems for assigning these numbers. No single encoding could contain enough characters: for example, the European Union alone requires several different encoding to cover all its languages. Even for a single language like English no single encoding was adequate for all the letters, punctuation, and technical symbols in common use.
These encoding systems also conflict with one another. That is, two encodings can use the same number for two different characters, or use different numbers for the same character. Any given computer (especially servers) needs to support many different encodings; yet whenever data is passed between different encodings or platforms, that data always runs the risk of corruption.
Unicode is changing all that!
Unicode provides a unique number for every character, no matter what the platform, no matter what the program, no matter what the language. The Unicode Standard has been adopted by such industry leaders as Apple, HP, IBM, JustSystems, Microsoft, Oracle, SAP, Sun, Sybase, Unisys and many others. Unicode is required by modern standards such as XML, Java, ECMAScript (JavaScript), LDAP, CORBA 3.0, WML, etc., and is the official way to implement ISO/IEC 10646. It is supported in many operating systems, all modern browsers, and many other products. The emergence of the Unicode Standard, and the availability of tools supporting it, are among the most significant recent global software technology trends.
Incorporating Unicode into client-server or multi-tiered applications and websites offers significant cost savings over the use of legacy character sets. Unicode enables a single software product or a single website to be targeted across multiple platforms, languages and countries without re-engineering. It allows data to be transported through many different systems without corruption.
About the Unicode Consortium
The Unicode Consortium is a non-profit organization founded to develop, extend and promote use of the Unicode Standard, which specifies the representation of text in modern software products and standards. The membership of the consortium represents a broad spectrum of corporations and organizations in the computer and information processing industry. The consortium is supported financially solely through membership dues. Membership in the Unicode Consortium is open to organizations and individuals anywhere in the world who support the Unicode Standard and wish to assist in its extension and implementation.
Saturday, April 24, 2010
Brain tumour's 'grow-or-go' switch found
Washington, March 12 (ANI): American researchers have discovered the brain tumour switch responsible for the 'grow-or-go' phenomenon.
Cancer cells in brain tumours have to adjust to periods of low energy or die. When energy levels are high, tumour cells grow and multiply but when levels are low, the cells grow less and migrate more.
Scientists at the Ohio State University Comprehensive Cancer Center-Arthur G. James Cancer Hospital and Richard J. Solove Research Institute discovered that a molecule called miR-451 directs the change, and that the change is accompanied by slower cell proliferation and an increase in cell migration.
This behaviour was closely associated to the cancer's ability to invade and spread. Thus, the molecule might be used as a biomarker to predict how long patients with the brain tumour glioblastoma multiforme will survive and may serve as a target to develop drugs to fight these tumors.
The researchers found that glioblastoma cells shift from their typical means of metabolizing glucose, a sugar brought by the bloodstream and usually used for energy, to an alternate means that consumes resources within the cell.
Co-author Dr. E. Antonio Chiocca, professor and chair of Neurological Surgery at Ohio State, said: "Our study reveals how brain tumor cells adapt to their surroundings and survive conditions that might fatally starve them of energy.
"We have discovered that glioblastoma cells use miR451 to sense the availability of a nutrient - glucose.
"Levels of miR-451 directly shut down the engine of the tumor cell if there in no glucose or rev it up if there is lots of glucose. This important insight suggests that this molecule might be useful as a biomarker to predict a glioblastoma patient's prognosis, and that it might be used as a target to develop drugs to fight these tumors."
The tumours are highly invasive, which makes them difficult to remove surgically, and respond poorly to radiation therapy and chemotherapy.
Average survival for patients is 14 months after diagnosis.
MiR-451 belongs to a class of molecules called microRNA, which play a key role in regulating the levels of proteins that cells make. Changes in levels of these molecules are a feature of many cancers, according to the researchers.
Principal investigator Sean Lawler, assistant professor of neurological surgery, said: "The change in miR-451 expression enabled the cells to survive periods of stress caused by low glucose, and it causes them to move, perhaps enabling them to find a better glucose supply.
"The migration of cancer cells from the primary tumor, either as single cells or as chains of cells, into the surrounding brain is a real problem with these tumors. By targeting miR-451, we might limit the tumor's spread and extend a patient's life."
For the study, Lawler, Chiocca, Jakub Godlewski, the postdoctoral fellow who was the first author of the study, and their team first compared microRNA levels in migrating and nonmigrating human glioblastoma multiforme cells. The analysis suggested an important role for miR-451.
Experiments with living cells demonstrated that high levels of glucose correlated with high levels of the molecule, and that this promotes a high rate of tumor-cell proliferation. Low glucose levels, on the other hand, demonstrated cell proliferation and increased cell migration.
Moreover, when the scientists boosted levels of the molecule in migrating cells, it slowed migration 60 percent, and, after 72 hours, almost doubled the rate of cell proliferation compared with controls.
Interestingly, when they forced an increase in miR-451 levels, the cells quickly died, suggesting a possible role in therapy.
Analyses of patient tumours demonstrated that three of five had elevated levels of the molecule. Finally, the researchers compared the survival in 16 patients with high miR-451 and 23 patients with low levels. Those with high levels of the molecule had an average survival of about 280 days while those with low levels lived an average of about 480 days.
Chiocca said: "This suggests that molecule may be a useful prognostic marker."
The findings of the study have appeared in the March 12 issue of the journal Molecular Cell. (ANI)
Cancer cells in brain tumours have to adjust to periods of low energy or die. When energy levels are high, tumour cells grow and multiply but when levels are low, the cells grow less and migrate more.
Scientists at the Ohio State University Comprehensive Cancer Center-Arthur G. James Cancer Hospital and Richard J. Solove Research Institute discovered that a molecule called miR-451 directs the change, and that the change is accompanied by slower cell proliferation and an increase in cell migration.
This behaviour was closely associated to the cancer's ability to invade and spread. Thus, the molecule might be used as a biomarker to predict how long patients with the brain tumour glioblastoma multiforme will survive and may serve as a target to develop drugs to fight these tumors.
The researchers found that glioblastoma cells shift from their typical means of metabolizing glucose, a sugar brought by the bloodstream and usually used for energy, to an alternate means that consumes resources within the cell.
Co-author Dr. E. Antonio Chiocca, professor and chair of Neurological Surgery at Ohio State, said: "Our study reveals how brain tumor cells adapt to their surroundings and survive conditions that might fatally starve them of energy.
"We have discovered that glioblastoma cells use miR451 to sense the availability of a nutrient - glucose.
"Levels of miR-451 directly shut down the engine of the tumor cell if there in no glucose or rev it up if there is lots of glucose. This important insight suggests that this molecule might be useful as a biomarker to predict a glioblastoma patient's prognosis, and that it might be used as a target to develop drugs to fight these tumors."
The tumours are highly invasive, which makes them difficult to remove surgically, and respond poorly to radiation therapy and chemotherapy.
Average survival for patients is 14 months after diagnosis.
MiR-451 belongs to a class of molecules called microRNA, which play a key role in regulating the levels of proteins that cells make. Changes in levels of these molecules are a feature of many cancers, according to the researchers.
Principal investigator Sean Lawler, assistant professor of neurological surgery, said: "The change in miR-451 expression enabled the cells to survive periods of stress caused by low glucose, and it causes them to move, perhaps enabling them to find a better glucose supply.
"The migration of cancer cells from the primary tumor, either as single cells or as chains of cells, into the surrounding brain is a real problem with these tumors. By targeting miR-451, we might limit the tumor's spread and extend a patient's life."
For the study, Lawler, Chiocca, Jakub Godlewski, the postdoctoral fellow who was the first author of the study, and their team first compared microRNA levels in migrating and nonmigrating human glioblastoma multiforme cells. The analysis suggested an important role for miR-451.
Experiments with living cells demonstrated that high levels of glucose correlated with high levels of the molecule, and that this promotes a high rate of tumor-cell proliferation. Low glucose levels, on the other hand, demonstrated cell proliferation and increased cell migration.
Moreover, when the scientists boosted levels of the molecule in migrating cells, it slowed migration 60 percent, and, after 72 hours, almost doubled the rate of cell proliferation compared with controls.
Interestingly, when they forced an increase in miR-451 levels, the cells quickly died, suggesting a possible role in therapy.
Analyses of patient tumours demonstrated that three of five had elevated levels of the molecule. Finally, the researchers compared the survival in 16 patients with high miR-451 and 23 patients with low levels. Those with high levels of the molecule had an average survival of about 280 days while those with low levels lived an average of about 480 days.
Chiocca said: "This suggests that molecule may be a useful prognostic marker."
The findings of the study have appeared in the March 12 issue of the journal Molecular Cell. (ANI)
Full form of Virus
VIRUS = = VITAL INFORMATION RESOURCE UNDER SIEGE
Detail about Computer virus :
A computer virus is a type of malicious software program ("malware") that, when executed, replicates itself by modifying other computer programs and inserting its own code. Infected computer programs can include, as well, data files, or the "boot" sector of the hard drive. When this replication succeeds, the affected areas are then said to be "infected" with a computer virus.
Virus writers use social engineering deceptions and exploit detailed knowledge of security vulnerabilities to initially infect systems and to spread the virus. The vast majority of viruses target systems running Microsoft Windows, employing a variety of mechanisms to infect new hosts, and often using complex anti-detection/stealth strategies to evade antivirus software. Motives for creating viruses can include seeking profit (e.g., with ransomware), desire to send a political message, personal amusement, to demonstrate that a vulnerability exists in software, for sabotage and denial of service, or simply because they wish to explore cybersecurity issues, artificial life and evolutionary algorithms.
Computer viruses currently cause billions of dollars' worth of economic damage each year, due to causing system failure, wasting computer resources, corrupting data, increasing maintenance costs, etc. In response, free, open-source antivirus tools have been developed, and an industry of antivirus software has cropped up, selling or freely distributing virus protection to users of various operating systems.As of 2005, even though no currently existing antivirus software was able to uncover all computer viruses (especially new ones), computer security researchers are actively searching for new ways to enable antivirus solutions to more effectively detect emerging viruses, before they have already become widely distributed.
The term "virus" is also commonly, but erroneously, used to refer to other types of malware. "Malware" encompasses computer viruses along with many other forms of malicious software, such as computer "worms", ransomware, trojan horses, keyloggers, rootkits, spyware, adware, malicious Browser Helper Object (BHOs) and other malicious software. The majority of active malware threats are actually trojan horse programs or computer worms rather than computer viruses. The term computer virus, coined by Fred Cohen in 1985, is a misnomer. Viruses often perform some type of harmful activity on infected host computers, such as acquisition of hard disk space or central processing unit (CPU) time, accessing private information (e.g., credit card numbers), corrupting data, displaying political or humorous messages on the user's screen, spamming their e-mail contacts, logging their keystrokes, or even rendering the computer useless. However, not all viruses carry a destructive "payload" and attempt to hide themselves—the defining characteristic of viruses is that they are self-replicating computer programs which modify other software without user consent.
reference
Detail about Computer virus :
A computer virus is a type of malicious software program ("malware") that, when executed, replicates itself by modifying other computer programs and inserting its own code. Infected computer programs can include, as well, data files, or the "boot" sector of the hard drive. When this replication succeeds, the affected areas are then said to be "infected" with a computer virus.
Virus writers use social engineering deceptions and exploit detailed knowledge of security vulnerabilities to initially infect systems and to spread the virus. The vast majority of viruses target systems running Microsoft Windows, employing a variety of mechanisms to infect new hosts, and often using complex anti-detection/stealth strategies to evade antivirus software. Motives for creating viruses can include seeking profit (e.g., with ransomware), desire to send a political message, personal amusement, to demonstrate that a vulnerability exists in software, for sabotage and denial of service, or simply because they wish to explore cybersecurity issues, artificial life and evolutionary algorithms.
Computer viruses currently cause billions of dollars' worth of economic damage each year, due to causing system failure, wasting computer resources, corrupting data, increasing maintenance costs, etc. In response, free, open-source antivirus tools have been developed, and an industry of antivirus software has cropped up, selling or freely distributing virus protection to users of various operating systems.As of 2005, even though no currently existing antivirus software was able to uncover all computer viruses (especially new ones), computer security researchers are actively searching for new ways to enable antivirus solutions to more effectively detect emerging viruses, before they have already become widely distributed.
The term "virus" is also commonly, but erroneously, used to refer to other types of malware. "Malware" encompasses computer viruses along with many other forms of malicious software, such as computer "worms", ransomware, trojan horses, keyloggers, rootkits, spyware, adware, malicious Browser Helper Object (BHOs) and other malicious software. The majority of active malware threats are actually trojan horse programs or computer worms rather than computer viruses. The term computer virus, coined by Fred Cohen in 1985, is a misnomer. Viruses often perform some type of harmful activity on infected host computers, such as acquisition of hard disk space or central processing unit (CPU) time, accessing private information (e.g., credit card numbers), corrupting data, displaying political or humorous messages on the user's screen, spamming their e-mail contacts, logging their keystrokes, or even rendering the computer useless. However, not all viruses carry a destructive "payload" and attempt to hide themselves—the defining characteristic of viruses is that they are self-replicating computer programs which modify other software without user consent.
reference
Facial paralysis
18-year-old Priya Gopal woke up in the morning with watery eyes and a sensation of acute pain on one side of her face. Believing it to be an eye infection, she went to an ophthalmologist, who gave her some eye drops. But these made no difference: The symptoms increased, and her facial muscles felt looser.
It was only after consulting a dentist and a physician that Priya ended up at a neurologist's office. Here she was shocked to hear that she had the symptoms of facial nerve paralysis or Bell's Palsy, in which the ability to control facial muscles on the affected side is temporarily lost. Which of us would imagine that pain or twitching on the face indicates facial paralysis?
"The symptoms of Bell's Palsy, which is the most common cause of facial paralysis, usually show up on one side of the face. There could be a loss of taste on the front of the tongue and an increase in the perception of sound in the ear on the affected side of the face. If the symptoms occur on the both sides of the face, this is usually due to other generalised nerve or muscle disorder such as Sarcoidosis," says Dr Praveen Gupta, consultant neurologist, Artemis Health Institute.
Facial paralysis can rob a person of the ability to smile, blink eyes, express emotions, hear or taste. This happens due to the inflammation of facial nerves or when regions within the brain through which the facial nerve passes are affected. A complete or partial loss of voluntary facial movements may occur, depending on the cause.
"The doctor usually determines whether the nerves in the forehead are involved in the facial paralysis to determine if the lesion is in the upper motor neuron component of the facial nerve, or the lower one," says Dr Renu Achtani, senior consultant, neurology, Fortis Hospital.
MANY CAUSES
THOUGH there are a number of serious causes which can lead to facial paralysis such as stroke, Moebius syndrome or Myasthenia Gravis. Occasionally, however, something as simple as an ear infection can also affect the facial nerves.
"Chronic ear infection may sometimes result from an infection of the mastoid bone, which is located in the inner ear. At times this may lead to facial paralysis. The problem can be taken care of by controlling the infection," says Dr Ashish Srivastava, consultant neurologist, Rockland Hospital.
Apart from this, infections in the brain or in the parotid glands (key pathways for the facial nerve, located in the upper part of each cheek) can also lead to facial paralysis. However, the most common cause of facial paralysis remains Bell's Palsy, which affect two in 10,000 people. The only reassuring fact about Bell's Palsy is that it is a temporary paralysis and most patients recover in a few weeks or a month unless the symptoms are severe or the treatment is delayed.
Though many blame herpes simplex virus for causing Bell's Palsy, there has been no established clinical study to prove this connection. Other common causes of facial paralysis are stroke, brain tumour and trauma.
Unlike in Bell's Palsy, in facial paralysis caused by a stroke the eye on the affected side can be closed and the forehead can be wrinkled. The severity of facial paralysis caused by a stroke depends on whether there is a blockage of an artery to the brain or whether the vessels of the brain have haemorrhaged.
"In facial paralysis caused by a stroke, it's the speech and the face that gets affected. It's important to rush a person who has suffered the stroke to the hospital within 4 hours so that the part of the brain where the blood flow is interrupted can be restored by the treatment," says Dr Gupta.
A tumour is one of the serious causes of facial paralysis. It develops gradually with symptoms such as headaches, hearing loss and seizures.
"Sometimes the facial nerves get entangled into the tumour and are damaged permanently during the attempt to excise the tumour surgically," says Dr Achtani. The severity of damage to the nerves depends on the size of the tumour and the stage of diagnosis. Trauma can also cause injury to the facial nerve in many ways.
In case of serious brain injury, the facial nerve fibers can be affected as they course through the brain and brain stem. A fracture through the temporal bone, the bone which houses the middle and inner ear, can also fracture the bony canal of the facial nerve.
TREATMENT IS EFFECTIVE
Don't get scared by the word steroids if you have been struck by Bell's Palsy. Steroids tablet will help you recover completely without any long-term problems with facial muscles.
According to the research done at the University of Toronto in Canada and published in the Journal of the American Medical Association in 2009, taking steroid tablets improves the chances of having a complete recovery from Bell's Palsy, whether the symptoms are moderate or severe, as it reduces inflammation and protect the nerves and muscles from further damage.
Taking antiviral drugs as well may help as they work against the virus which possibly causes the infection. "The treatment of Bell's Palsy can be very effective if administered within a few days of occurrence, so it is very important to consult the doctor in time. Usually, 70 to 80 percent of the patients respond well to the treatment which include steroids, anti- viral, galvanic stimulation and physiotherapy," says Dr Srivastava.
Since in Bell's Palsy the eye doesn't shut, complications such as corneal ulcers and infections may occur. "It's important to take good care of the eye and put the eye drops regularly as they control the dryness of eyes," emphasises Dr Srivastava.
In case of trauma or stroke the treatment usually depends on the region of the brain which has been affected. Physiotherapy also plays a vital role in the treatment of facial paralysis. While medicines may control the symptoms in the beginning, physiotherapy strengthens the muscles and brings back the lost mobility.
"In the beginning the stimulation to the face is given by the machine so that it doesn't sag but the patient has to be very proactive and do the exercises at home till the time the facial nerves work finely," says Dr Renu.
All Windows Run Commands
Full run commands
- Accessibility Controls --> access.cpl
- Add Hardware Wizard --> hdwwiz.cpl
- Add/Remove Programs --> appwiz.cpl
- Administrative Tools --> control admintools
- Automatic Updates --> wuaucpl.cpl
- Bluetooth Transfer Wizard --> fsquirt
- Calculator --> calc
- Certificate Manager --> certmgr.msc
- Character Map --> charmap
- Check Disk Utility --> chkdsk
- Clipboard Viewer --> clipbrd
- Command Prompt --> cmd
- Component Services --> dcomcnfg
- Computer Management --> compmgmt.msc
- Date and Time Properties --> timedate.cpl
- DDE Shares --> ddeshare
- Device Manager --> devmgmt.msc
- Direct X Control Panel (If Installed)* --> directx.cpl
- Direct X Troubleshooter --> dxdiag
- Disk Cleanup Utility --> cleanmgr
- Disk Defragment --> dfrg.msc
- Disk Management --> diskmgmt.msc
- Disk Partition Manager --> diskpart
- Display Properties --> control desktop
- Display Properties --> desk.cpl
- Display Properties (w/Appearance Tab Preselected) --> control color
- Dr. Watson System Troubleshooting Utility --> drwtsn32
- Driver Verifier Utility --> verifier
- Event Viewer --> eventvwr.msc
- File Signature Verification Tool --> sigverif
- Findfast --> findfast.cpl
- Folders Properties --> control folders
- Fonts --> control fonts
- Fonts Folder --> fonts
- Free Cell Card Game --> freecell
- Game Controllers --> joy.cpl
- Group Policy Editor (XP Prof) --> gpedit.msc
- Hearts Card Game --> mshearts
- Iexpress Wizard --> iexpress
- Indexing Service --> ciadv.msc
- Internet Properties --> inetcpl.cpl
- IP Configuration (Display Connection Configuration) --> ipconfig /all
- IP Configuration (Display DNS Cache Contents) --> ipconfig /displaydns
- IP Configuration (Delete DNS Cache Contents) --> ipconfig /flushdns
- IP Configuration (Release All Connections) --> ipconfig /release
- IP Configuration (Renew All Connections) --> ipconfig /renew
- IP Configuration (Refreshes DHCP & Re-Registers DNS) --> ipconfig /registerdns
- IP Configuration (Display DHCP Class ID) --> ipconfig /showclassid
- IP Configuration (Modifies DHCP Class ID) --> ipconfig /setclassid
- Java Control Panel (If Installed) --> jpicpl32.cpl
- Java Control Panel (If Installed) --> javaws
- Keyboard Properties --> control keyboard
- Local Security Settings --> secpol.msc
- Local Users and Groups --> lusrmgr.msc
- Logs You Out Of Windows --> logoff
- Mcft Chat --> winchat
- Minesweeper Game --> winmine
- Mouse Properties --> control mouse
- Mouse Properties --> main.cpl
- Network Connections --> control netconnections
- Network Connections --> ncpa.cpl
- Network Setup Wizard --> netsetup.cpl
- Notepad --> notepad
- Nview Desktop Manager (If Installed) --> nvtuicpl.cpl
- Object Packager --> packager
- ODBC Data Source Administrator --> odbccp32.cpl
- On Screen Keyboard --> osk
- Opens AC3 Filter (If Installed) --> ac3filter.cpl
- Password Properties --> password.cpl
- Performance Monitor --> perfmon.msc
- Performance Monitor --> perfmon
- Phone and Modem Options --> telephon.cpl
- Power Configuration --> powercfg.cpl
- Printers and Faxes --> control printers
- Printers Folder --> printers
- Private Character Editor --> eudcedit
- Quicktime (If Installed) --> QuickTime.cpl
- Regional Settings --> intl.cpl
- Registry Editor --> regedit
- Registry Editor --> regedit32
- Remote Desktop --> mstsc
- Removable Storage --> n******mgr.msc
- Removable Storage Operator Requests --> n******oprq.msc
- Resultant Set of Policy (XP Prof) --> rsop.msc
- Scanners and Cameras --> sticpl.cpl
- Scheduled Tasks --> control schedtasks
- Security Center --> wscui.cpl
- Services --> services.msc
- Shared Folders --> fsmgmt.msc
- Shuts Down Windows --> shutdown
- Sounds and Audio --> mmsys.cpl
- Spider Solitare Card Game --> spider
- SQL Client Configuration --> cliconfg
- System Configuration Editor --> sysedit
- System Configuration Utility --> msconfig
- System File Checker Utility (Scan Immediately) --> sfc /scannow
- System File Checker Utility (Scan Once At Next Boot) --> sfc /scanonce
- System File Checker Utility (Scan On Every Boot) --> sfc /scanboot
- System File Checker Utility (Return to Default Setting) --> sfc /revert
- System File Checker Utility (Purge File Cache) --> sfc /purgecache
- System File Checker Utility (Set Cache Size to size x) --> sfc /cachesize=x
- System Properties --> sysdm.cpl
- Task Manager --> taskmgr
- Telnet Client --> telnet
- User Account Management --> nusrmgr.cpl
- Utility Manager --> utilman
- Windows Firewall --> firewall.cpl
- Windows Magnifier --> magnify
- Windows Management Infrastructure --> wmimgmt.msc
- Windows System Security Tool --> syskey
- Windows Update Launches --> wupdmgr
- Windows XP Tour Wizard --> tourstart
- Wordpad --> write
What does 3G wireless mean for you?
After being postponed several times in the last two years, the long-awaited auction process for 3G services is well on its way and mobile subscribers in India can soon expect to see a revolutionary change in the way telecom services will be available to them.
3G is all about speed, speed, and more speed! 3G represents a paradigm shift from the voice-centric world of the previous generations of wireless networks to the multimedia-centric world of 3G. Simply put, it will shift the focus from the ears to the eyes. It is the next generation of wireless network technology that provides high speed bandwidth (high data transfer rates) to handheld mobile devices. The high data transfer rates will allow 3G networks to offer multimedia services combining voice and data.
3G services will seamlessly combine superior voice quality telephony, high-speed mobile IP services, IT, rich media, and offer diverse content. The characteristics of 3G services will ensure 'always on' Internet download speeds of up to 2Mbps.
There's no doubt that 3G represents the next big thing in mobility. Just as broadband Internet access took over from conventional dial-up and radically changed the way you were able to use the Internet from conventional desktop and laptop computers, 3G holds the same promise for mobile users accessing and leveraging the Internet while on the move. Suddenly, the hours travelling on the road or rail or waiting at airports or in between meetings will become productive and entertaining for all of us.
3G services, apart from giving us capacity and speed, will give us the benefits of multitasking. Consider ourselves as wireless knowledge workers who will have far greater flexibility, efficiency and speed of response to a multitude of demanding situations in real time, while we are on the move. We shall soon be capable of getting an exciting range of mobile services such as mobile office services, virtual banking, home shopping, video-conferencing, rich multimedia with streaming audio & video, email and instant messaging with audio/ video clips, online entertainment like mobile TV and many more services which not only will be location-based but will also include personalised services where specific content can be pushed to users based on individual needs!
Video conferencing
Face-to-face video calling between compatible 3G mobile phones: Users will be able to see each other as they talk on the move. Think of it as a webcam you carry in your pocket. Look at the time and costs (what with the increasing complexity of traffic and oil prices) you will save by not travelling for one-on-one meetings!
TV & video on demand
A user will be able to watch TV channels on their mobile phone. Just imagine the thrill of being able to watch the crucial sports matches or your favourite 'soap' on your mobile when you are stuck in the middle of a traffic jam. You can also 'demand' a movie or a TV programme of your choice!
Social networking
Social networking has seen a monumental influx of users over the past several years as websites like YouTube, MySpace, Facebook and Twitter have gained widespread traction in India and mind you, it is not only restricted to the youth. I know a fare share of users who are the not-so-welcome parents. These sites typically allow you to post and share videos, pictures and comments of your personal lives to a central site that can then be accessed by the general public or select users. Millions of users around the globe are accessing these websites, downloading and uploading photos and videos as well as communicating online via their mobile devices.
With faster speeds of 3G services soon coming to your doorstep, imagine being able to connect to Facebook & Twitter and a host of all those social networking and instant messaging without any delays. Post your 'status' every hour or Tweet constantly even while on the move.
Location-based services
A location-based service (LBS) is an information service provided by telecom operators that is accessible by your mobile phone. LBS services utilise the geographic position of the mobile phone to provide location information to the user. Uses of LBS include mapping and navigation applications and social networking services based on location and presence technologies either embedded in the handset or placed in the network.
LBS services can be used in a variety of contexts, such as healthcare, professional and personal life. LBS services include services to identify a location of a person or object, such as finding the nearest ATM machine, business or the location of a friend or employee. LBS services include parcel tracking and vehicle tracking services. They include personalised weather services, traffic alerts and even location-based games. LBS services can include mobile commerce when taking the form of coupons or advertising directed at customers based on their current location. Retailers can deploy applications that recognise potential consumers' presence within a given geographic area-for example, as they walk past a store- and deliver highly personalised multimedia marketing content to entice them into the store. Beware all you impulsive shoppers!
The consumer benefits of 3G are clear: downloading songs in mere seconds, surfing the Internet at fast speeds, or streaming live television and satellite radio broadcasts. But how does this next-generation wireless protocol stack up when it comes to the critical area of costs? The 3G spectrum will hopefully be auctioned successfully, and while its primary purpose was to contribute to the further development of the telecom sector and benefit the Indian subscribers, it has also captured attention for its probable positive impact on India's fiscal health and its exchange rate. Just as the intense competitive environment that exists amongst the 2G service providers has ensured that cellular services in India are available at amongst the lowest tariff rates in the world, let us hope that 3G services will also follow suit and likewise be available at an affordable price so that the masses can enjoy the multitude of benefits of 3G.
If you want to join the party, make sure that you buy a 3G compatible mobile phone, the next time you are in the market to replace your faithful but soon to be obsolete 2G device.
3G is all about speed, speed, and more speed! 3G represents a paradigm shift from the voice-centric world of the previous generations of wireless networks to the multimedia-centric world of 3G. Simply put, it will shift the focus from the ears to the eyes. It is the next generation of wireless network technology that provides high speed bandwidth (high data transfer rates) to handheld mobile devices. The high data transfer rates will allow 3G networks to offer multimedia services combining voice and data.
3G services will seamlessly combine superior voice quality telephony, high-speed mobile IP services, IT, rich media, and offer diverse content. The characteristics of 3G services will ensure 'always on' Internet download speeds of up to 2Mbps.
There's no doubt that 3G represents the next big thing in mobility. Just as broadband Internet access took over from conventional dial-up and radically changed the way you were able to use the Internet from conventional desktop and laptop computers, 3G holds the same promise for mobile users accessing and leveraging the Internet while on the move. Suddenly, the hours travelling on the road or rail or waiting at airports or in between meetings will become productive and entertaining for all of us.
3G services, apart from giving us capacity and speed, will give us the benefits of multitasking. Consider ourselves as wireless knowledge workers who will have far greater flexibility, efficiency and speed of response to a multitude of demanding situations in real time, while we are on the move. We shall soon be capable of getting an exciting range of mobile services such as mobile office services, virtual banking, home shopping, video-conferencing, rich multimedia with streaming audio & video, email and instant messaging with audio/ video clips, online entertainment like mobile TV and many more services which not only will be location-based but will also include personalised services where specific content can be pushed to users based on individual needs!
Video conferencing
Face-to-face video calling between compatible 3G mobile phones: Users will be able to see each other as they talk on the move. Think of it as a webcam you carry in your pocket. Look at the time and costs (what with the increasing complexity of traffic and oil prices) you will save by not travelling for one-on-one meetings!
TV & video on demand
A user will be able to watch TV channels on their mobile phone. Just imagine the thrill of being able to watch the crucial sports matches or your favourite 'soap' on your mobile when you are stuck in the middle of a traffic jam. You can also 'demand' a movie or a TV programme of your choice!
Social networking
Social networking has seen a monumental influx of users over the past several years as websites like YouTube, MySpace, Facebook and Twitter have gained widespread traction in India and mind you, it is not only restricted to the youth. I know a fare share of users who are the not-so-welcome parents. These sites typically allow you to post and share videos, pictures and comments of your personal lives to a central site that can then be accessed by the general public or select users. Millions of users around the globe are accessing these websites, downloading and uploading photos and videos as well as communicating online via their mobile devices.
With faster speeds of 3G services soon coming to your doorstep, imagine being able to connect to Facebook & Twitter and a host of all those social networking and instant messaging without any delays. Post your 'status' every hour or Tweet constantly even while on the move.
Location-based services
A location-based service (LBS) is an information service provided by telecom operators that is accessible by your mobile phone. LBS services utilise the geographic position of the mobile phone to provide location information to the user. Uses of LBS include mapping and navigation applications and social networking services based on location and presence technologies either embedded in the handset or placed in the network.
LBS services can be used in a variety of contexts, such as healthcare, professional and personal life. LBS services include services to identify a location of a person or object, such as finding the nearest ATM machine, business or the location of a friend or employee. LBS services include parcel tracking and vehicle tracking services. They include personalised weather services, traffic alerts and even location-based games. LBS services can include mobile commerce when taking the form of coupons or advertising directed at customers based on their current location. Retailers can deploy applications that recognise potential consumers' presence within a given geographic area-for example, as they walk past a store- and deliver highly personalised multimedia marketing content to entice them into the store. Beware all you impulsive shoppers!
The consumer benefits of 3G are clear: downloading songs in mere seconds, surfing the Internet at fast speeds, or streaming live television and satellite radio broadcasts. But how does this next-generation wireless protocol stack up when it comes to the critical area of costs? The 3G spectrum will hopefully be auctioned successfully, and while its primary purpose was to contribute to the further development of the telecom sector and benefit the Indian subscribers, it has also captured attention for its probable positive impact on India's fiscal health and its exchange rate. Just as the intense competitive environment that exists amongst the 2G service providers has ensured that cellular services in India are available at amongst the lowest tariff rates in the world, let us hope that 3G services will also follow suit and likewise be available at an affordable price so that the masses can enjoy the multitude of benefits of 3G.
If you want to join the party, make sure that you buy a 3G compatible mobile phone, the next time you are in the market to replace your faithful but soon to be obsolete 2G device.
Subscribe to:
Posts (Atom)